
Warehouse Wi-Fi FAQ: What are the Most Common ‘Pain Points’ with Warehouse Networks?
Warehouse WiFi, WiFi, WiFi Solutions,
Warehouses are fast-paced environments where many pressure points in supply chains converge. When these pressure points are factored into space design and [...]

Analysis of Multiple PSK in the context of WPA3
Business WiFi,
The ability to use multiple passphrases on a single Service Set Identifier (SSID) has been in place for more than a decade; [...]

With cyber attacks on a continued increase, every industry should be looking long and hard at how it is safeguarding itself – [...]

Why SMBs need advanced security solutions
Business WiFi,
Cyber Security is a top priority for small and medium businesses, who can no longer get by with standard solutions. SMBs need [...]
What’s the Difference Between SD-WAN and SASE?
Network Management, Network Security,
Software-Defined Wide Area Networking (SD-WAN) and Secure Access Service Edge (SASE) are two prominent technologies that have emerged to address the evolving [...]

Digital transformation is vital for businesses today in staying competitive. With companies looking to save time and reduce costs, replacing outdated, legacy [...]
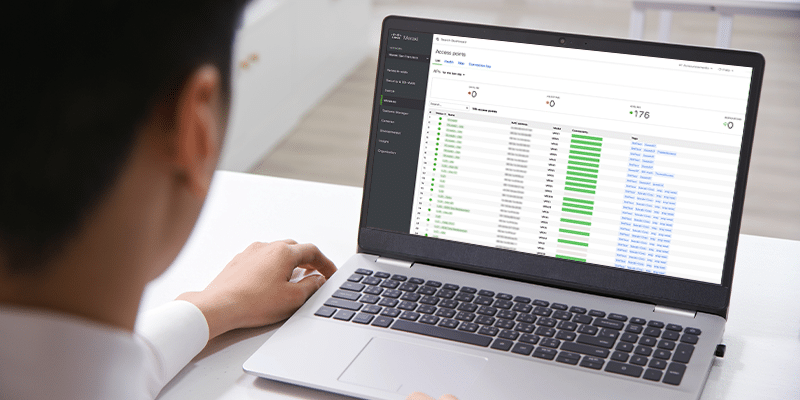
Intelligent, intuitive, scalable and centralised, the dashboard is one of the biggest benefits of a Cisco Meraki solution. There are so many [...]
How can next-gen networking reduce the cost of network management?
Network Management,
Today’s advanced networking technologies and architectures don’t just aim to enhance the performance of networks; they also have the capacity to transform [...]

Why Superior Wi-Fi Networks will Increasingly Underpin the Most Efficient Warehouses
Warehouse WiFi,
With the increasing reliance of warehouses on technology, it is no surprise that as IT advances, the opportunity to close gaps in [...]